Investigators probing the recent ransacking of International Monetary Fund computers have concluded the attack was carried out by cyber spies connected to China, according to two people close to the investigation.
Computer specialists have spent several weeks piecing together information about the attack, which the IMF disclosed on June 8.
 Evidence pointing to China includes an analysis of the attack methods, as well as the electronic trail left by hackers as they removed large quantities of documents from the IMF’s computers. The multistaged attack, which used U.S.-based servers as part of their equipment, ended on May 31, people involved in the investigation said on the condition they not be identified because they aren’t authorized to speak about it.
Evidence pointing to China includes an analysis of the attack methods, as well as the electronic trail left by hackers as they removed large quantities of documents from the IMF’s computers. The multistaged attack, which used U.S.-based servers as part of their equipment, ended on May 31, people involved in the investigation said on the condition they not be identified because they aren’t authorized to speak about it.
Their conclusion is likely to be a major test for the new IMF chief,Christine Lagarde, who this month appointed Chinese economist Zhu Min as deputy managing director, giving China a much expanded role in the institution.
“There are some very big questions about the role that China wants to play in the global economic system and what role it can play given some of its behavior,” said C. Fred Bergsten, who heads the Washington-based Peterson Institute for International Economics.
The timing of the attack and China’s lobbying for more influence at the Fund appear to overlap, creating a potentially embarrassing situation for China among the IMF’s 186 other members, including the U.S.
Scope of Attack
IMF officials have said little publicly about the scope of the attack or its origins, citing the on-going nature of the investigation, which involves outside forensics experts and the fund’s own information-technology team.
Yesterday, David Hawley, an IMF spokesman, said the investigation was not yet complete. “We’re continuing to investigate what happened and assess” what was taken, he said.
William Murray, another IMF spokesman, declined to comment on the source of the attack.
Wang Baodong, a spokesman for the Chinese embassy in Washington, said in an e-mail that hacking is “an international issue” affecting dozens of countries and “willfully relating such cases with China is irresponsible.”
People familiar with the incident said that the hackers were able to download a large quantity of documents from dozens of computers on the IMF’s network, which was first infected when an employee downloaded a file containing a piece of sophisticated spying software that quickly spread.
Internal IMF e-mails obtained by Bloomberg News suggest fund officials completed an inventory of those documents by the middle of July, including an “operational impact assessment.” The results have not been made public.
IMF Internal E-Mails
In an internal e-mail sent to staff, Patrick Hinderdael, the IMF’s adviser to the chief information officer, said the attack occurred in at least two phases, and that no activity by the hackers has been detected since the end of May. In the first phase, the attackers grabbed “a general sweep” of recent files then returned for a second wave of downloads, Hinderdael said.
Hackers have learned to use sophisticated methods to hide their identities, including hijacking servers in other countries to launch an attack. Forensics specialists have similarly advanced techniques to cut through the fog. Those include analyzing the code left behind in networks and tracing patterns in multiple attacks that may use the same infrastructure.
Dominique Strauss-Kahn, the head of the IMF, was arrested in New York City on sexual assault charges on May 14 and resigned four days later, setting off an international search for a new director including demands by emerging economies that one of their own lead the fund. Lagarde, the former French finance minister, was appointed to fill the position beginning July 5.
Lagarde’s Cyber Experience
Lagarde has had experience with similar cyber attacks. In March, the French finance ministrysaid its computer network had been hacked and that documents related the French presidency of the G-20 were stolen. The magazine Paris Match quoted a French official saying the information was redirected to servers in China.
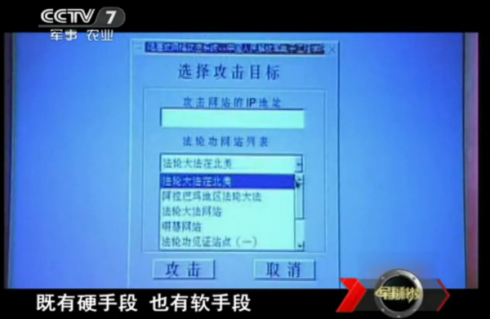
Google Inc. (GOOG) has said its computers were attacked by Chinese-based hackers in late 2009, along with the networks of at least 20 other companies. According to diplomatic cables posted by the website WikiLeaks, U.S. defense and intelligence officials have documented the operations of sophisticated cyber spies operating from China over several years.
“As an intelligence professional, I stand back in absolute awe and wonderment at the Chinese espionage effort against the United States of America,” Gen. Michael Hayden, the former CIA director, said at cyber security conference last year. “It is magnificent in its breath, its depth and its efficiency.”
China’s Clout
China, which is driving global economic growth, has been gaining clout in international organizations. In 2008 Justin Lin, a Taiwan-born scholar who defected to China, became the first World Bank chief economist from outside Europe and Lagarde created a new position for Zhu at the IMF, giving China access to a top management post for the first time.
A few months earlier, China obtained the third-largest voting share at the fund after the 187 member countries agreed to better reflect the growing weight of emerging markets in the world’s economy.
China needs to decide whether it will be a cooperative global power or pursue national interests that can be disruptive, Bergsten said.
“The cyber security issue is a very big part of that but it’s only part of a broader mosaic,” he said.
Global Cornerstone
The IMF is a cornerstone institution in the global economic system, managing financial crises around the world. The fund’s computers are likely to contain confidential documents on the fiscal health of many countries.
“The IMF holds some of most valuable data anywhere,” said Josh Shaul, chief technology officer with Application Security, Inc., a cyber security firm based in New York City, NY.
The financial status of countries is critical information for major nation-state investors or holders of sovereign debt, he said.
Hinderdael said in an e-mail to IMF staff that the attack was not related to identity theft or commercial fraud, another indication the intruders weren’t ordinary cyber thieves.
“According to our experts’ assessment, the information contained in our e-mail, document management, human resource, and financial systems has not been compromised,” Hinderdael said in the e-mail.
via China-Based Spies Said to Be Behind Hacking of IMF in Investigators’ View – Bloomberg.